As drones become increasingly common in both commercial and recreational spaces, the need to manage unauthorized or malicious flights has never been greater. For security professionals, facility managers, and law enforcement, two primary counter-drone strategies dominate the conversation: drone detection and drone jamming.
While both aim to mitigate the risks posed by rogue drones, they operate on fundamentally different principles, serve distinct purposes, and come with vastly different legal and operational implications. Understanding the differences between detection and jamming is essential for anyone designing a comprehensive counter-UAS (Unmanned Aircraft System) strategy.
This article provides a full comparison of drone detection and drone jamming, exploring how each works, their respective strengths and weaknesses, and how they can be used together for layered security.
What Is Drone Detection?
Drone detection refers to the process of identifying, locating, and sometimes classifying unmanned aircraft within a protected airspace—without interfering with the drone’s operation. Detection is purely passive or non-intrusive; it gathers intelligence about the threat but does not actively neutralize it.
Common Detection Technologies
-
Radio Frequency (RF) Analysis:
RF sensors passively scan the electromagnetic spectrum for the unique communication signatures used by drones and their controllers. They can identify the drone’s make and model, location, and even the pilot’s position. RF detection is often the first line of defense because it works regardless of visibility. -
Radar Systems:
Traditional radar detects drones by tracking moving objects in the sky. Modern counter-drone radars are optimized for small, low-altitude, slow-moving targets (often called “low, slow, small” or LSS targets). Radar provides precise positional data but may struggle to distinguish drones from birds. -
Electro-Optical (EO) and Infrared (IR) Cameras:
Cameras provide visual confirmation and tracking. EO cameras work in daylight, while IR cameras detect heat signatures at night or in poor weather. Advanced systems use AI-powered video analytics to automatically classify detected objects as drones. -
Acoustic Sensors:
Acoustic arrays detect the unique sound signatures of drone motors and propellers. While effective in quiet environments, they are less reliable in noisy urban settings.
What Detection Provides
-
Threat awareness and early warning
-
Pilot location tracking (via RF triangulation)
-
Forensic data for post-incident analysis
-
Continuous monitoring without physical interference
What Is Drone Jamming?
Drone jamming is an active countermeasure that disrupts the communication links between a drone and its operator. Unlike detection, which simply observes, jamming directly intervenes to neutralize the threat by forcing the drone into a predetermined fail-safe state—typically landing or returning to home.
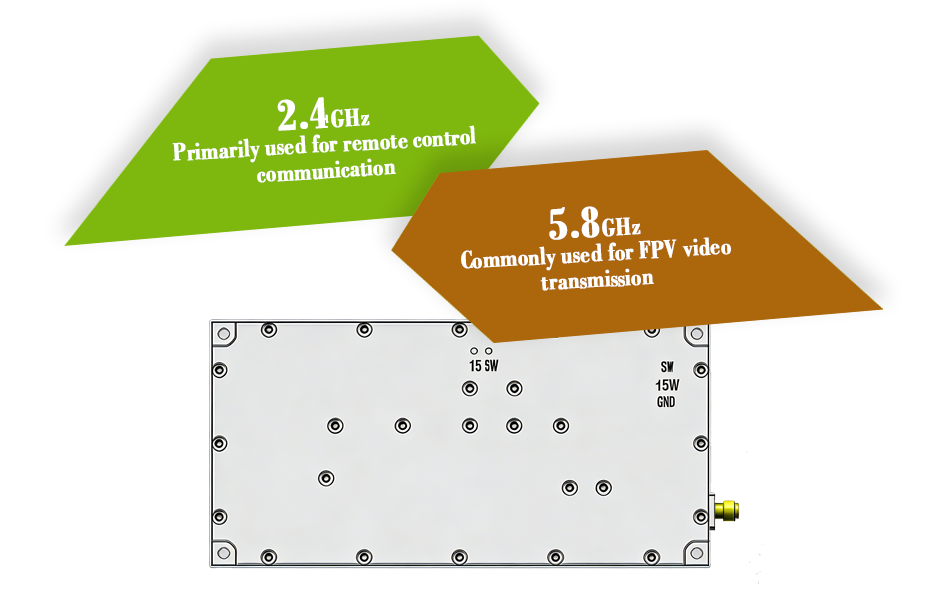
As explored in previous articles, jamming typically targets either the RF control link (2.4GHz/5.8GHz) or the GNSS navigation link (GPS, GLONASS, etc.), or both simultaneously.
Common Jamming Approaches
-
RF Jamming: Overwhelms the control signal with high-power noise, severing the pilot’s ability to command the drone.
-
GNSS Jamming: Disrupts satellite positioning signals, causing the drone to lose situational awareness and often forcing it into a hover or landing state.
-
Spoofing (Advanced): A more sophisticated technique that broadcasts fake GNSS or control signals to deceive the drone into following false commands.
What Jamming Provides
-
Immediate neutralization of an active threat
-
Forced landing or return-to-home of unauthorized drones
-
Rapid response capability for time-sensitive situations
Head-to-Head Comparison
| Feature | Drone Detection | Drone Jamming |
|---|---|---|
| Approach | Passive / non-intrusive | Active / intrusive |
| Purpose | Identify, locate, and track threats | Neutralize threats by disrupting control |
| Interference with Drone | None | Severs control link or navigation |
| Legal Status | Generally legal for private and commercial use | Illegal for civilians in most countries (e.g., FCC restrictions) |
| Operational Range | Varies by sensor; can be several kilometers | Typically line-of-sight; range depends on transmit power |
| Collateral Impact | Minimal; may occasionally misidentify objects | Can interfere with nearby Wi-Fi, Bluetooth, or emergency communications |
| Evidence Collection | Provides forensic data, video footage, and logs | Provides no visual evidence; neutralizes rather than documents |
| Use Case | Continuous monitoring, perimeter security, threat assessment | Active response to imminent threats after positive identification |
Strengths and Weaknesses
Detection Strengths
-
Legally permissible in most jurisdictions for private and commercial entities
-
Continuous operation without disrupting legitimate activities
-
Provides actionable intelligence including pilot location and drone type
-
Builds evidence for legal or investigative follow-up
Detection Weaknesses
-
Does not stop the drone—detection alone cannot prevent intrusion or malicious action
-
Sensor limitations—no single sensor type is perfect; RF may miss autonomous drones, radar may confuse drones with birds, cameras require clear line-of-sight
Jamming Strengths
-
Immediate effect—neutralizes the threat within seconds of activation
-
Effective against most consumer and commercial drones that rely on standard RF and GNSS links
-
Can be deployed as a final layer of defense after detection confirms an unauthorized intrusion
Jamming Weaknesses
-
Legally restricted—unauthorized use can result in heavy fines or criminal penalties in many countries
-
Collateral interference—may affect other devices operating on the same frequencies
-
No forensic value—jamming stops the drone but does not capture evidence about the operator or the incident
-
Limited effectiveness against autonomous drones that do not rely on continuous RF control
Detection and Jamming: Better Together
While detection and jamming are often presented as alternatives, the most effective counter-drone strategies employ both in a layered approach.
A typical layered security framework might look like this:
-
Detection Layer: RF sensors and radar continuously monitor the airspace, providing early warning of drone activity.
-
Identification Layer: EO/IR cameras zoom in to visually confirm the drone type and assess intent.
-
Decision Point: Security personnel evaluate the threat based on location, flight behavior, and risk level.
-
Jamming Layer: If the drone poses an imminent threat and legal authorization exists, a jammer is activated to force a landing or return-to-home.
-
Forensic Layer: Post-incident, detection logs and video footage are preserved for investigation and legal action.
This layered approach ensures that jamming is used only when necessary—and only after positive identification—while detection provides the situational awareness needed to make informed decisions.
Which One Is Right for Your Organization?
Choosing between detection and jamming—or combining both—depends on several factors:
-
Legal Authority: If your organization is not a government or military entity, jamming is likely off the table. In that case, detection alone may be your only legal option.
-
Risk Profile: High-risk facilities such as airports, nuclear plants, or government buildings may have pathways to authorized jamming deployment. Lower-risk sites may rely on detection and procedural responses.
-
Budget: Detection systems vary widely in cost, from affordable RF sensors to multi-sensor integrated platforms. Jamming equipment itself is not prohibitively expensive, but the legal and operational constraints often make it inaccessible to private entities.
-
Operational Goals: If your goal is to monitor and document intrusions, detection suffices. If you need to actively stop a threat in real time, jamming becomes necessary—provided it is legally permissible.
Conclusion
Drone detection and drone jamming serve complementary but fundamentally different roles in counter-UAS operations. Detection provides awareness, intelligence, and evidence without interfering with the drone. Jamming provides active neutralization but comes with significant legal restrictions and potential collateral effects.
For most private organizations, a robust detection system is the only legally viable option. For authorized government and security entities, integrating detection with jamming creates a comprehensive defense capable of both identifying threats and stopping them when necessary.
Ultimately, the choice between detection and jamming is not simply a technical one—it is a legal, operational, and strategic decision that must align with both regulatory requirements and the specific security needs of the protected airspace.