The rapid proliferation of drones has brought unprecedented convenience to industries ranging from logistics to cinematography. However, it has also introduced significant security challenges. Unauthorized drones hovering over airports, government buildings, critical infrastructure, or private events pose serious risks to safety, privacy, and national security. In response, anti-drone technology—also known as counter-unmanned aircraft systems (C-UAS)—has emerged as a critical defense layer. This article explores how these systems detect, track, and neutralize rogue drones.
The Three Pillars of Anti-Drone Defense
Effective counter-drone operations typically follow a three-step framework: detect, identify, and defeat. Each stage relies on specialized technologies working in concert.
1. Detection: Finding the Threat
Before you can stop a drone, you need to know it is there. Detection systems use various sensors to locate unauthorized UAVs:
-
Radar: Traditional radar systems can detect drones at long ranges, but small consumer drones are difficult to distinguish from birds or other objects. Modern micro-Doppler radar analyzes the unique rotational signature of drone propellers to improve accuracy.
-
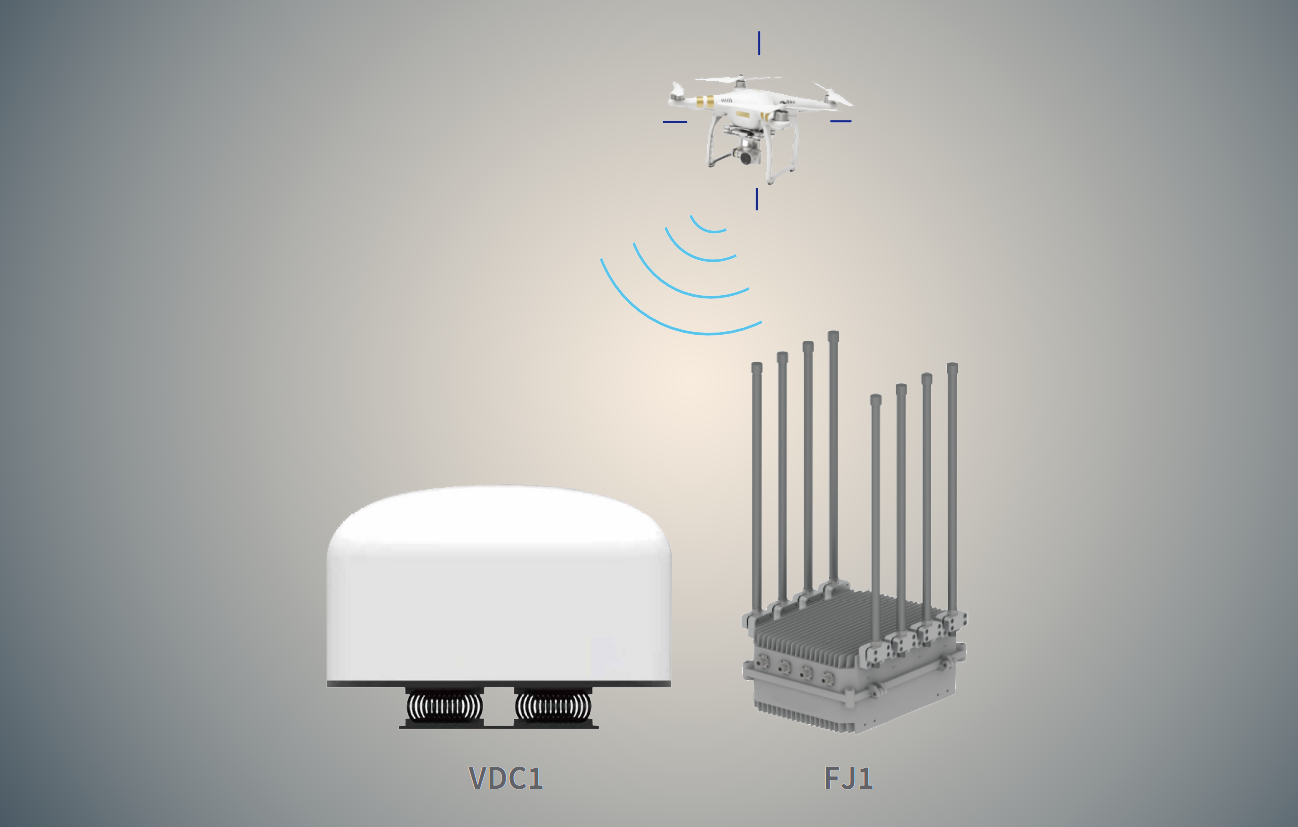
Radio Frequency (RF) Sensors: These devices passively scan the electromagnetic spectrum for control signals, telemetry, and video transmission commonly used by drones (e.g., 2.4 GHz, 5.8 GHz, 4G/5G). RF sensors can often identify the drone model and even locate the pilot’s position.
-
Electro-Optical (EO) and Infrared (IR) Cameras: Once a potential threat is detected by radar or RF sensors, high-definition cameras with thermal imaging are used to visually confirm the drone’s presence, track its movement, and classify its type—day or night.
-
Acoustic Sensors: These systems use arrays of microphones to recognize the unique sound signatures of different drone motors and propellers. While effective in quiet environments, they can be overwhelmed by ambient noise in urban settings.
2. Identification: Friend or Foe
Not all drones are threats. Distinguishing between authorized and unauthorized UAVs is crucial to avoid disrupting legitimate operations. Many advanced C-UAS platforms integrate remote identification (Remote ID) decoding capabilities. Remote ID is a digital broadcast standard that transmits the drone’s ID, location, and pilot location. If a drone fails to broadcast Remote ID or if its flight path violates restricted airspace, it is flagged as unauthorized.
3. Defeat: Neutralizing the Threat
Once a drone is confirmed as unauthorized and poses a risk, countermeasures are deployed. Defeat methods fall into two broad categories: non-kinetic (soft kill) and kinetic (hard kill).
Non-Kinetic Countermeasures: Soft Kill
Soft kill methods disable the drone without physically destroying it. These are often preferred in crowded or sensitive environments where collateral damage must be minimized.
RF Jamming
The most common anti-drone technique is radio frequency jamming. Jammers emit high-power noise on the frequencies drones use for control and video transmission—typically 2.4 GHz and 5.8 GHz. By overwhelming the legitimate signal, the jammer severs the link between the drone and its pilot.
Most consumer and commercial drones are programmed with failsafe behaviors. When they lose the control signal, they will either:
-
Return to Home (RTH): Automatically fly back to their takeoff point.
-
Land in Place: Descend immediately.
-
Hover: Remain stationary until the battery runs out.
Jamming is effective against a wide range of drones, but it has limitations. Drones operating on frequency-hopping spread spectrum (FHSS) require wideband jammers that cover entire frequency ranges. Additionally, jamming affects all nearby devices operating on the same frequencies, which can disrupt legitimate Wi-Fi or Bluetooth communications.
GNSS/GPS Spoofing
Many drones rely heavily on Global Navigation Satellite System (GNSS) signals for positioning, navigation, and stabilization. GNSS spoofing involves broadcasting fake satellite signals to trick the drone into believing it is somewhere else.
A spoofer can:
-
Force the drone to land at a designated “safe zone.”
-
Create a virtual geofence that the drone cannot cross.
-
Disorient the drone, causing it to enter a failsafe mode.
Because spoofing does not involve brute-force signal suppression, it can be more discreet than jamming. However, it requires precise technical execution and is generally used by law enforcement and military-grade systems.
Protocol Exploitation
Some advanced counter-drone systems exploit vulnerabilities in the communication protocols used by specific drone manufacturers. By reverse-engineering the handshake process, these systems can inject commands into the drone’s control link—such as forcing a landing or disabling the motors—without triggering the drone’s standard failsafe behaviors.
Kinetic Countermeasures: Hard Kill
When non-kinetic methods are insufficient or when the drone poses an imminent threat (such as a weaponized UAV), kinetic solutions are employed to physically destroy or capture the drone.
Net Guns and Capture Drones
Net guns can be handheld or mounted on larger drones. They fire a weighted net that entangles the rogue drone’s propellers, causing it to fall or be carried away. Capture drones—sometimes called “interceptor drones”—are themselves UAVs equipped with nets or grappling mechanisms. They are deployed to physically intercept and retrieve unauthorized drones in mid-air.
Directed Energy Weapons
High-power microwave (HPM) systems and high-energy lasers represent the cutting edge of anti-drone technology.
-
High-Power Microwaves: These systems emit a burst of electromagnetic energy that fries the drone’s electronic circuitry, causing it to drop from the sky. HPM can affect multiple drones simultaneously and is effective against swarms.
-
High-Energy Lasers: Lasers deliver concentrated thermal energy to a specific point on the drone, burning through critical components such as wings, motors, or batteries. Lasers offer precision engagement but typically require a clear line of sight and significant power infrastructure.
Projectile-Based Systems
In military and high-security applications, kinetic solutions include kinetic interceptors (small guided missiles) or even conventional firearms equipped with specialized anti-drone ammunition. These methods are reserved for extreme threats due to the risk of collateral damage from falling debris.
Layered Defense: The Most Effective Approach
No single anti-drone technology is perfect. RF jamming may be ineffective against autonomously flying drones that do not rely on a continuous control link. Spoofing may fail against drones using encrypted GNSS signals. Physical interceptors are expensive and risk ground damage.
The most robust security frameworks employ a layered defense strategy:
-
Detect using radar and RF sensors.
-
Identify via Remote ID or behavioral analysis.
-
Warn the operator with directional signals or alerts.
-
Disable using non-kinetic methods like jamming or spoofing.
-
Destroy as a last resort with kinetic systems.
Conclusion
Anti-drone technology has evolved rapidly to keep pace with the growing number of unauthorized UAVs in our skies. From passive RF sensors that detect drone activity to jammers that sever control links and directed energy weapons that physically neutralize threats, modern C-UAS systems offer a range of tools for protecting sensitive airspace. The key to effective defense lies in a layered approach that combines detection, identification, and graduated response options—ensuring that security measures are both effective and proportionate to the threat.
As drone technology continues to advance, so too will the countermeasures designed to stop them. Staying informed about both sides of this technological arms race is essential for security professionals, policymakers, and anyone responsible for protecting critical assets.