The rapid proliferation of commercial drones has revolutionized industries from cinematography to agriculture. Unfortunately, it has also created new vulnerabilities for critical infrastructure, military bases, airports, and correctional facilities. This has driven significant investment in Counter-Unmanned Aircraft Systems (C-UAS), specifically integrated drone detection and jamming systems.
These systems combine radar, radio frequency (RF) analysis, and electronic attack capabilities into a single command and control interface. However, due to the technical and legal complexities of electronic warfare, end-users often have pressing questions about how these systems work and what they can realistically achieve.
Below, we address the most common questions posed by security managers, system integrators, and defense personnel regarding drone detection and jamming technology.
1. What is the Difference Between Detection and Jamming?
This is the most fundamental question in C-UAS.
-
Detection is passive. It involves “listening” for drone signals or “watching” the sky with radar. A detection module identifies the presence, location, and sometimes the model of a drone. It does not transmit any energy; it only receives. This makes detection legally safe and covert.
-
Jamming is active. It involves transmitting high-power radio frequency energy to sever the communication link between the drone and its pilot or to spoof its GPS navigation. Jamming is an electronic countermeasure that results in the drone landing, returning home, or hovering in place.
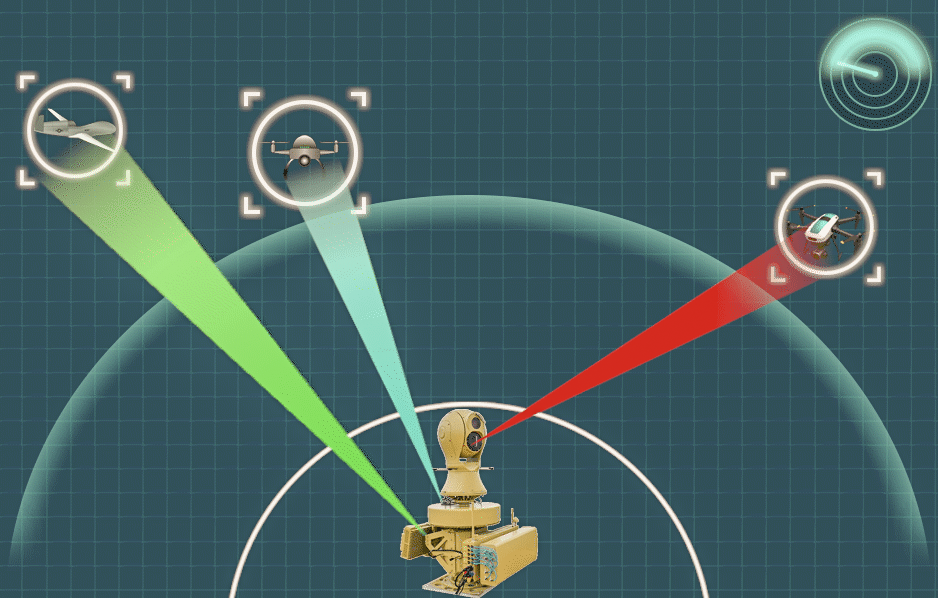
An integrated system links these two functions. The detection sensor cues the jammer, ensuring the jammer only activates when a verified threat is present and only on the specific frequency required.
2. How Does the System Detect a Drone Before I Can See or Hear It?
Human senses are poor drone detectors. By the time you hear the “buzz” of propellers, the drone is likely already within 100 meters—often too late for a meaningful response.
Modern detection systems rely on RF Passive Detection and Micro-Doppler Radar:
-
RF Sensors: These scan the electromagnetic spectrum for the unique communication signatures of common drone protocols (OcuSync, Lightbridge, Crossfire, etc.). They can detect a drone and its pilot’s location from several kilometers away, often before the drone even takes off, by identifying the remote controller’s telemetry link.
-
Radar: Specialized 3D radars are tuned to detect small, slow-moving objects (low RCS) that traditional aircraft radar filters out as “clutter.” Advanced algorithms distinguish a bird from a quadcopter based on micro-Doppler shifts caused by spinning propellers.
3. What Happens to the Drone When It Is Jammed?
This is a concern for safety and liability. A properly designed jammer does not make a drone fall out of the sky like a rock. Instead, the system forces a fail-safe protocol.
When a drone loses contact with its controller signal (2.4 GHz / 5.8 GHz) or its GPS lock (L1/L2 bands), its internal firmware executes a pre-programmed response:
-
Return-to-Home (RTH): Most common. The drone climbs to a safe altitude (avoiding obstacles) and flies back to its recorded takeoff point.
-
Land Immediately: The drone descends vertically where it is.
-
Hover: The drone holds position until the battery dies and then lands.
An integrated system allows the operator to choose the most appropriate “defeat mechanism” based on the environment (e.g., forcing Return-to-Home over a crowded stadium is safer than forcing an immediate landing).
4. Is It Legal to Use a Drone Jammer?
This is the most complex and jurisdiction-dependent question.
In most countries (including the United States, Canada, the UK, and EU member states), the use of RF jamming by private citizens or commercial entities is strictly illegal. Jammers interfere with licensed radio spectrum and potentially public safety communications. Only specific federal agencies (military, law enforcement, or national security) typically have the legal authority to deploy active jamming countermeasures.
For commercial and private security, the solution is Detection-Only or Takeover Technology. Detecting a drone and alerting local law enforcement is legal. Some systems offer non-jamming mitigation like protocol manipulation (taking control of the drone if it uses a known, unencrypted protocol), but this remains a legally grey area in many regions. Always consult with local telecommunications and aviation authorities before deploying any active C-UAS measure.
5. How Long Can the System Operate Continuously?
This question directly relates to our previous discussion on heat management and efficiency.
An integrated system is a network of high-power electronics. Detection sensors are low-power and can run 24/7 indefinitely. The jammer module is the limiting factor. High-power broadband jammers generate significant heat. As outlined in our guide to thermal management, an entry-level system might only sustain a 10-20% duty cycle (e.g., 2 minutes on, 10 minutes off) before thermal throttling reduces output power.
Professional, military-grade integrated systems utilize active liquid cooling or advanced GaN amplifier designs to achieve 100% duty cycles, meaning they can jam continuously for hours until the drone threat is neutralized or the generator runs out of fuel.
6. Can These Systems Jam Swarms of Drones?
The threat landscape is shifting from single nuisance drones to coordinated swarms. A standard wideband barrage jammer works well against one or two drones but becomes inefficient against a swarm spread across a wide bandwidth.
To counter swarms, integrated systems now employ Electronic Beam Steering and AI-Driven Resource Allocation.
-
Phased Array Jammers: Instead of blasting noise in all directions (wasting energy and causing collateral interference), these systems create a precise, high-power beam and “paint” each drone sequentially for milliseconds. This time-slicing allows one system to engage dozens of targets in rapid succession.
-
Smart Jamming: AI analyzes the swarm’s protocol and identifies the weakest link (often the swarm coordination signal). By targeting only that specific channel, the entire swarm can be disrupted without jamming the entire spectrum.
7. What is the Effective Range?
Range is not a single number; it depends on the environment and the system component.
| Component | Typical Range | Limiting Factor |
|---|---|---|
| RF Detection | 5 – 20 km | Line of Sight (curvature of earth) & Urban RF Noise |
| Radar Detection | 2 – 5 km | Radar Cross Section (size of drone) |
| RF Jamming | 1 – 3 km | Transmit Power & Antenna Gain |
Crucial Note: Jamming range is not symmetrical. A jammer must overcome the signal strength of the drone’s remote controller. You might detect a drone at 10km, but you cannot effectively jam it until it is within 2km because the signal from the pilot’s controller is relatively weak compared to the jammer’s output.
8. Will It Interfere with My Wi-Fi or Nearby Hospitals?
Collateral interference is a primary concern for responsible deployment. Yes, a poorly designed or improperly aimed broadband jammer will interfere with Wi-Fi (which shares the 2.4 GHz and 5 GHz bands) and potentially GPS devices in the immediate vicinity.
High-end integrated systems mitigate this through:
-
Sector Antennas: Using directional antennas to focus energy upward and in a specific azimuth, minimizing the “spillover” to ground level.
-
Smart Blanking: The system can be programmed to avoid jamming specific emergency frequencies used by local police or medical telemetry.
Conclusion
Integrated drone detection and jamming systems are powerful tools for airspace security, but they are not simple “plug-and-play” devices. Understanding the interplay between passive detection and active jamming, respecting legal constraints, and managing thermal performance are essential for effective deployment.
Whether you are protecting a border, a power plant, or a public event, the key is selecting a system that offers precision rather than brute force. As the drone threat evolves, so too must the intelligence and efficiency of the countermeasures we deploy.